Authentication
This provider requires authentication.- cilium_base_endpoint: The base endpoint of the cilium hubble relay (required: True, sensitive: False)
In workflows
This provider can’t be used as a “step” or “action” in workflows. If you want to use it, please let us know by creating an issue in the GitHub repository.Topology
This provider pulls topology to Keep. It could be used in correlations and mapping, and as a context for alerts and incidents.Overview
The Cilium provider leverages Hubble’s network flow data to automatically discover service dependencies and build a topology map of your Kubernetes applications.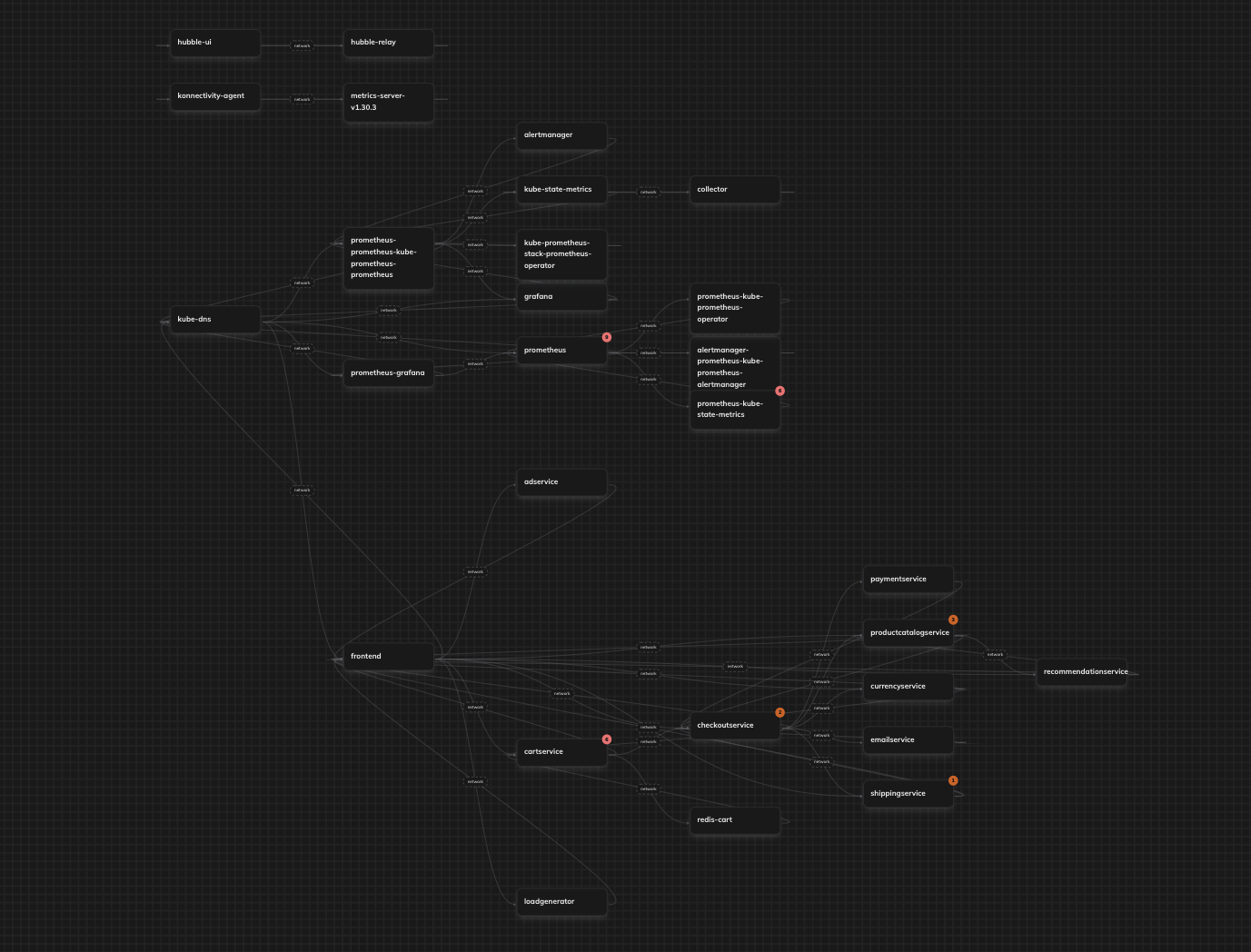
Authentication Parameters
| Parameter | Description | Example |
|---|---|---|
cilium_base_endpoint | The base endpoint of the Cilium Hubble relay | localhost:4245 |
Outputs
The provider returns topology information including:- Service names and their dependencies
- Namespace information
- Pod labels and cluster metadata
- Network-based relationships between services
Service Discovery Logic
The provider identifies services using the following hierarchy:- Workload name (if available)
- Kubernetes labels (
k8s:app=ork8s:app.kubernetes.io/name=) - Pod name (stripped of deployment suffixes)
Requirements
- A running Kubernetes cluster with Cilium installed
- Hubble enabled and accessible via gRPC
- Network visibility (flow logs) enabled in Cilium
Limitations
- Only captures active network flows between pods
- Service discovery is limited to pods with proper Kubernetes labels
- Requires direct access to the Hubble relay endpoint
Useful Links
Google Kubernetes Engine specific
If you are using a GKE cluster, you cannot connect Keep to the Google-managed hubble-relay directly because:- hubble-relay operates only in secure mode,
- hubble-relay requires client certificate authentication.
hubble-relay-insecure.gke-managed-dpv2-observability:80 address.